AnyTree For Any Git
In the world of software development, security has never been more paramount. As dependency trees grow more intricate, the threats to the integrity of software supply chains also expand. Recognizing these challenges, AnyTree has been pioneering tools and methodologies to ensure this integrity. So much so that today developers can rely on GOSH AnyTree to guarantee the security of their software delivery.
We also find that offering this guarantee through the use of the GOSH platform alone, as in a monolith, is very restrictive. This is why GOSH is proud to announce that AnyTree now works with any Git storage. Developers worldwide use GitHub, GitLab or private Git servers as their primary code repository, so now there’s no need to change their workflows, no need to upload any private or public repositories to any external service, and they can keep using their favorite package managers, and be sure that their software supply chain is secured by GOSH AnyTree.
Today, the keystones of scientific research are reproducibility (which is arguably more important even than repeatability) and verifiability. It's not always possible to reproduce everything, but scientific research of worth should be able to do so to some degree. But when we talk about software a problem arises: We are talking about reproducibility in a world where we don't have pure function in real life, and so, at a high level, reproducibility and verifiability are dependent entirely on the very code they are supposed to reproduce and verify. Deep SBOM on AnyTree is a tool designed to solve this cyclical problem. And it isn't just a fancier version of the traditional SBOM.
A traditional SBOM offers a list — a static representation of software components. In contrast, the Deep SBOM provides developers with an unprecedented level of visibility. It's not just about identifying the components but ensuring that they reproduce precisely the same artifact every time they're built directly from their SBOM. The idea is simple yet profound: by detailing every step, every resource, and every dependency in the process as this process is ongoing, discrepancies become glaringly evident. Such transparency is vital because even minor deviations can open doorways to vulnerabilities. If it only works one way (as in: you create your artifact and then record what you use) there is always room for a mistake. Developers need to prove that the SBOM you get in the end includes the same artifact they got through the process of building. And there was no such tool that could produce an artifact from SBOM, until now.
AnyTree uses Deep SBOM that allows developers to see what they built and why
…and to reproduce the same result exactly
Currently, when developers use a SBOM, they can't really trust it. It already mitigates some threats, but not a lot of them. It's still vulnerable because they have no real guarantees that the SBOM is correct, which can be disastrous for security. With AnyTree, if developers use an empty SBOM and say: “Build me an artifact!” they will get an empty artifact or you will have an error. It depends on their policy, but either way they will get nothing that can threaten their system and that they are not aware of.
Consider the practical implications of this. In the conventional world, the SBOM is a snapshot. If the process of artifact creation is dynamic, there can always be discrepancies between two SBOMs. With Deep SBOM, however, everything a developer uses, precisely, step by step, can be reproduced in exactly the same way. And because there's an auditable trail from the source to the artifact, offering an undeniable guarantee that everything aligns, its correctness can be verified.
Usually this is when authors note that even with such rigorous checks and balances, there's always the human element.
Manually reviewing every line of code, every library, and every patch is exhausting and, frankly, unsustainable. Deep SBOM bridges the gap between manual audits and automated security. While developers can audit the entire code base, the efficiency of the Deep SBOM means they only need to verify its accuracy to ensure everything downstream is secure.
They can build an artifact in such a way that they split it into stages and can prove that at a certain point they didn’t use more than is required in any one stage.
How to use AnyTree on GitHub (Example for Rust)*
Run make install to build GOSH AnyTree tool
Generate sbom.json for your Rust project using Python script located under tools/python/generate-sbom.py
Note: either copy script to your cargo project and run `python3 generate-sbom.py` or check and configure variables in script
After running the script you should get the following output at the end
Updated SBOM written to sbom.json
And generated sbom.json file in the following format https://github.com/gosh-sh/anytree/blob/dev/tools/python/sbom.json
Now you can use sbom.json to build your app
anytree build sbom.json
After running the script you should get similar output at the end:
Successfully copied 15.8MB to
/home/user/.cache/anytree/builder/anytree-builder-69a20ddf-b0cf-46ea-923a-f208fcd8357a/target
And your artifacts will be accessible in this folder
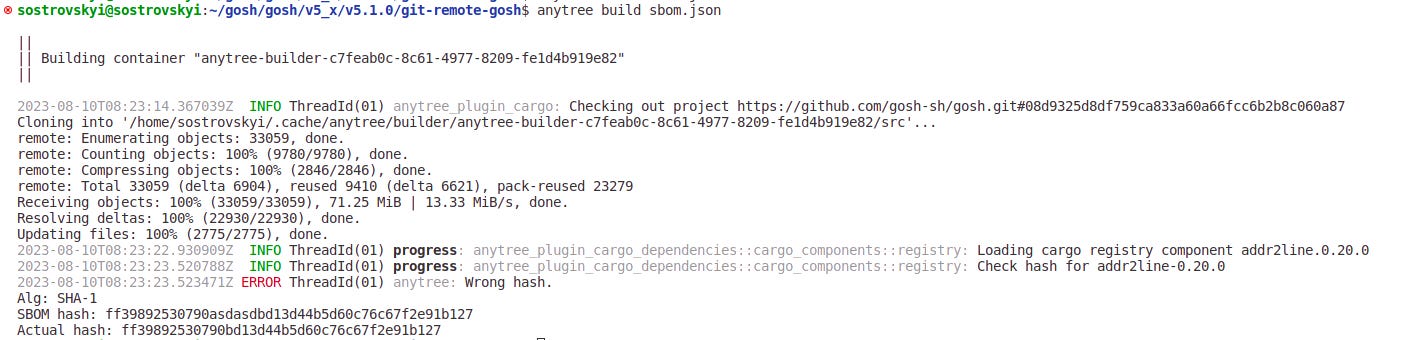
In the event of a hash mismatch error you will know that something is wrong when you see this:
*To use another programming language, please contact us directly
Functional usefulness of DeepSBOM can, of course, be extended with standard SBOM tools, and if you need any changes to the DeepSBOM format AnyTree supports extended compatibility with the tools you are using, just reach out to us.
It opens you a lot of possibilities to secure any set of dependencies, from which one can infer that the result is also secure by induction. Currently the problem is that this induction is not connected. Today, developers have pieces of the map, some of which show minefields, while others don’t; unless one has the whole picture, one cannot make global assumptions, only local ones. AnyTree is built to give developers a full image of everything they need to know about their software supply chain, including all potential dangers…
Now, Deep SBOM functionality is extended to every Git user.
It’s worth noting, however, that while the integration of AnyTree for Git offers an enhanced layer of security, it might not include the full array of features available on GOSH. But it's a start, especially for those who already trust their private Git repositories and signature setups, this integration provides an additional blanket of assurance. Immutable builds, detailed dependency trees, and a deeper dive into software components become accessible without the need for a drastic shift in infrastructure.
At the core of AnyTree’s philosophy is the idea that you shouldn't have to trust anyone, any tools provider for your software’s security. Using AnyTree on GOSH allows you to benefit from trustless signatures, so you don't need to actually trust any signature provider. These are guarantees that GOSH gives even if you take our word for it or not. But, if you already trust your private repository server, your signature set up, and your source code, then now you can use AnyTree to build your code, giving you immutable builds based on your trusted infrastructure, offering additional protection to your software supply chain, so that all bugs and intrusions to your repository will be recognized immediately. And if you don’t trust it enough — just use a GOSH repository instead, and complete the circle.